In kenya, the following are regulatory bodies that you need to know
-
NC4 a multi agency entity that has been mandated to coordinate the protection of Kenya's Cyber Space.
-
ODPC The Government agency that is mandated to ensure proper handling of personal data within Kenya.
-
KE CIRT The Kenya Computer Incident Response Team – Coordination Centre (National KE-CIRT/CC) was launched by the Government in 2014, order to mitigate cyber threats and foster a safer Kenyan cyberspace. The KE-CIRT detects, prevents and responds to various cyber threats targeted at the country on a 24/7 basis as well as act as link between Kenyan and international ICT service providers whose platforms may be used to perpetrate cybercrimes, this link extends to law enforcement Kenyan and International and the Judiciary.
-
KENET CERT is an Academic Sector CIRT, promotes awareness on cybersecurity incidences as well as coordinates and assists member institutions in responding effectively to cyber security threats and incidences. It is operated by the National Research and Education Network of Kenya. KENET-CERT works closely with Kenya's National CIRT coordination center (CIRT/CC)
-
Central Bank of Kenya is the Regulator of Banks in Kenya, The financial sector is way ahead in dealing with Cyber Security Risk given that the central bank issued a Cyber Security Guideline for Payment Service Providers in 2018. This guideline can be applied to the Computer Misuse and CyberCrime Act, 2024 (Critical Information Infrastructure and Cyber Crime Management)
Regulations affecting Cyber Security and Data
These are the regulations that you are supposed to comply by
- Data Protection Act, 2019
- Computer Misuse and Cyber Crimes Act, 2018
- Computer Misuse and CyberCrime Act, 2024 (Critical Information Infrastructure and Cyber Crime Management)
- The Kenya National Cyber Security Strategy
Guidelines
- NC4 Guidelines
- ODPC Guidelines
- Central bank of Kenya Guideline
Cyber Security Frameworks and Standards
Cyber Security is very wide, frameworks will enable you to manage and reduce cyber risks by providing a commin language and a systematic approach to identify threats and assets, protect the assets, detect cyber attacks as well as respond and recover from cyber attacks. The most common frameworks used to manage cyber security are
- ISO 27001
- NIST
- CSA
Introducing document FORM CMCA 6 which provides a template of the Audit Report. This is what the auditor will begin with checking, get ahead if the game on the compliance
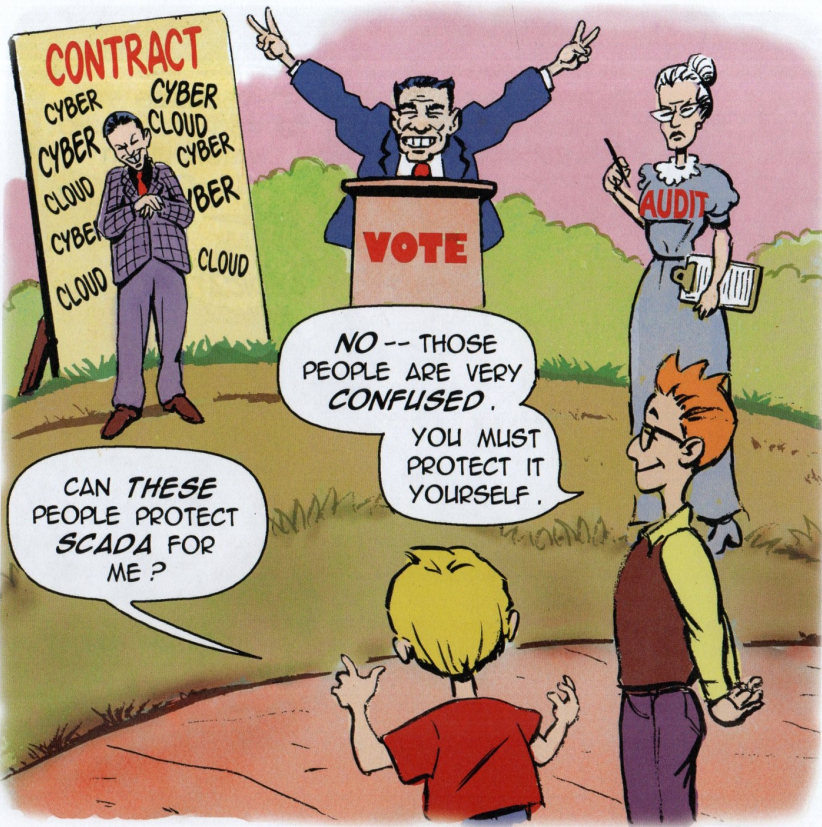
I have to make it clear, audits are meant to demonstrate compliance and it does not provide cyber security to your organization
References
- Lee, R. M. (n.d.). SCADA and Me: A Book for Children and Management.